VSHN.timer #44: Thunderspy Hits The Fan


Welcome to another VSHN.timer! Every Monday, 5 links related to Kubernetes, OpenShift, CI / CD, and DevOps; all stuff coming out of our own chat system, making us think, laugh, or simply work better.
This week we’re going to talk about the latest news in IT security. It’s a wild world out there.
1. Earlier this month Björn Ruytenberg made public the Thunderspy vulnerabilities, leading to (hang tight) nine practical exploitation scenarios. Here’s the scary part: this one affects any computer with Thunderbolt ports, providing stealth and absolute control, even though it requires physical access to the device. Really scary stuff, but a good example of responsible disclosure… and some not really ideal responses from various vendors.
https://thunderspy.io/
2. Speaking about security specialists, we found the story of Marcus Hutchins absolutely fascinating. Hutchins allegedly saved the Internet from what was, at the time, the worst cyberattack in history, a malware known as WannaCry. His story features Defcon, FBI agents, and the life of an otherwise unknown but utterly brilliant computer science student caught in the whirlwind of technology.
https://www.wired.com/story/confessions-marcus-hutchins-hacker-who-saved-the-internet/
3. Most of us log in and out of SSH connections all the time; but most importantly, here in VSHN many of us are also involved in setting and managing secure SSH connections for our customers. In any case, this guide to SSH properly and this list of SSH tips and tricks will surely teach you some new tricks.
https://gravitational.com/blog/how-to-ssh-properly/
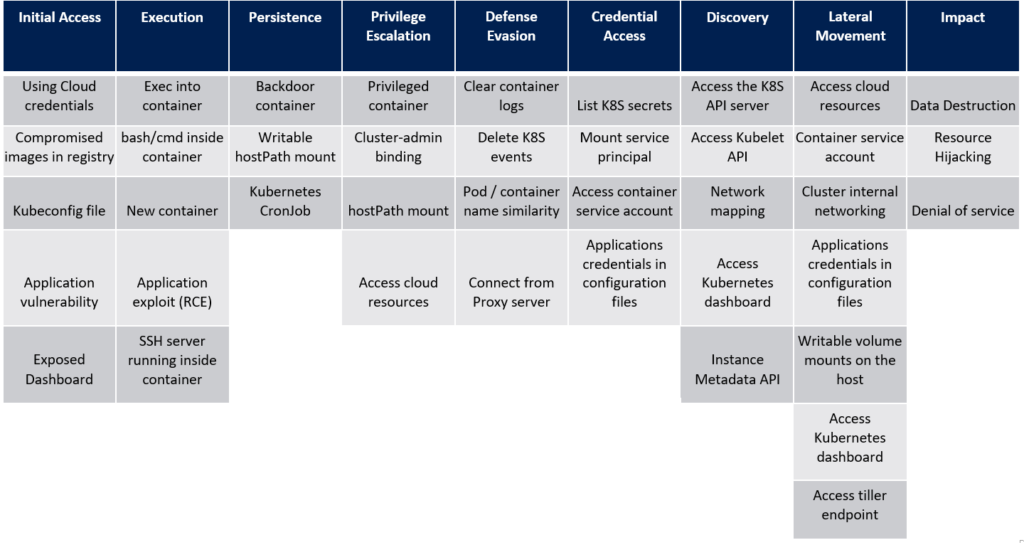
4. If you manage Kubernetes clusters, you might be asking yourself how to make sure that you haven’t forgotten some security configuration somewhere that might come back and bite you. Thankfully Microsoft has come up with an extensive attack matrix for Kubernetes which might provide some starting points for your investigation. And since we’re at it, you might also want to monitor the outbound traffic from your clusters as well.
https://www.microsoft.com/security/blog/2020/04/02/attack-matrix-kubernetes/
5. The tool of the week is the Managed Kubernetes Inspection Tool, used to validate several common security-related configuration settings of clusters and the objects contained therein. Given the astronomical number of configuration options in our clusters, this one is a must have in our toolbelts for sure.
https://github.com/darkbitio/mkit
How do you secure the perimeters around your IT infrastructure? Do you have any tips you would like to share with the community? Get in touch with us through the form at the bottom of this page, and see you next week for another edition of VSHN.timer.